Introduction: The New Frontier of Identity and Access for AI
As organizations deploy autonomous AI agents across their digital ecosystems, traditional identity and access management (IAM) frameworks—designed for predictable human users and deterministic workflows—are proving inadequate. AI agents operate with autonomy, non-deterministic behaviors, and the ability to act on behalf of humans. This shift demands a fundamentally different authorization model: one that seamlessly blends identity, delegation, real-time policy evaluation, and temporary, context-scoped permissions.
HashiCorp Vault, a leading secrets management and identity-based access solution, is answering this call. The company has announced native AI agent support, introducing a suite of capabilities tailored for the unique operational and security needs of autonomous systems. These features—currently in early access with select customers—address the pressing requirement for guardrails, fine-grained runtime authorization, clear attribution, and a standardized approach to securing AI agents across hybrid environments.
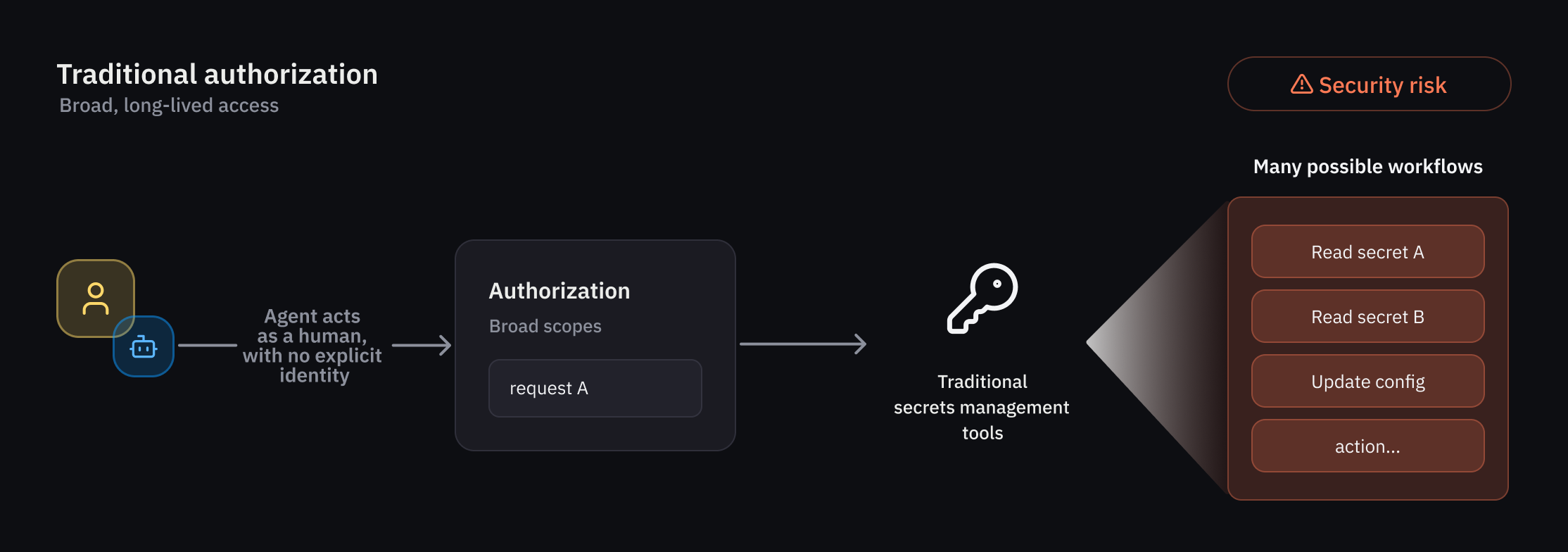
The Challenge: Traditional IAM Falls Short for Autonomous AI Agents
AI agents introduce actors that are not only non-human but also non-deterministic—their actions can vary based on context, learning, and external inputs. Traditional IAM models rely on pre-defined users, roles, and static permissions, which cannot accommodate the fluid, request-specific needs of an agentic workflow. Organizations using Vault have identified several critical gaps:
- Enforcing guardrails for agents that behave less predictably than humans or traditional non-human identities (NHIs).
- Requiring fine-grained authorization that can be evaluated at runtime and scoped to individual actions or workflows.
- Ensuring clear attribution and auditability for every action an agent performs on behalf of a user.
- Establishing a standardized security posture for AI agents across diverse environments and operational workflows.
These challenges drove HashiCorp to develop Vault capabilities specifically engineered for agentic workflows—capabilities that go beyond mere access control to deliver identity-aware, ephemeral, and auditable authorization.
Vault’s New AI Agent Capabilities
Vault’s new capabilities center on three pillars: an agent registry, identity-based policies, and per-request ephemeral authorization. Together, they form a comprehensive framework for managing AI agent identities, permissions, and oversight.
Agent Registry: A Dedicated Identity Primitive
The agent registry introduces a new identity primitive that allows developers to register and manage agent activity separately from human and traditional NHI identities. This separation is crucial for delegation flows, where an agent acts using an on-behalf-of (OBO) pattern from a human user, with explicit delegation and consent. By tracking this delegation transparently, the registry becomes the foundation for a dedicated lifecycle management system—covering registration, authorization, credential management, and observability. This ensures that every agent action is traceable back to its originating human principal.
Granular Identity-Based Policies for Least Privilege
Least-privilege access is a top priority for any IAM system, and it’s especially critical for agents whose behavior can be unpredictable. Vault addresses this through a rich set of policy-based runtime controls, enabling administrators to strictly govern agent activities. Because agent behavior is non-deterministic, Vault applies deterministic guardrails combined with per-request access control. When an agent operates in delegation mode—carrying the authority of a human user—Vault evaluates trust across multiple dimensions. This means the agent’s access to secrets and credentials is always context-aware, ensuring that even autonomous actions remain within tightly defined boundaries.
Ephemeral Authorization for Per-Request Control
One of the most powerful innovations is per-request ephemeral authorization. This reduces risk by granting temporary access rights that automatically expire after a specific task or timeframe. Instead of static, long-lived credentials, agents receive just-in-time permissions scoped to the precise transaction context. This approach aligns perfectly with the transient nature of agentic workflows, where a single request might span multiple systems and actions, but should never leave behind lingering privileges. Combined with the agent registry and identity policies, this creates a robust security model where authorization is dynamic, auditable, and tightly coupled to the agent’s identity and purpose.
Delegation and Auditability in Agentic Workflows
Auditability is a non-negotiable requirement for enterprise AI deployments. Vault’s new capabilities ensure that every action performed by an agent—whether initiated autonomously or on behalf of a human—is clearly attributed. The OBO delegation pattern is explicitly tracked, creating a chain of accountability that satisfies both security and compliance teams. This allows organizations to answer the critical question: “Who or what requested this action, and was it authorized at the moment of execution?” With the agent registry and policy engine, Vault provides the observability needed to detect anomalies, enforce governance, and maintain a clear audit trail in even the most dynamic agent environments.
Early Access and Public Beta Timeline
Select customers are currently evaluating these AI agent capabilities through an early access program. HashiCorp has announced that a broader public beta will be available in a future Vault release planned for this summer. Organizations interested in securing their AI agent deployments are encouraged to engage with the early access program or prepare for the upcoming beta to gain first-hand experience with these transformative security controls.
For a deeper look at the technical implementation, revisit the sections on agent registry, identity-based policies, and ephemeral authorization.